How To Choose A Web Hosting Provider For Your Website
There’s lots to consider when building a website for yourself or your business.
Near the top of your website to-do list should be choosing a web hosting provider. This is the server on which your website will live, which is akin to the neighborhood in which your home is built. You wouldn’t build a house in a dangerous, overcrowded area, would you? Well, same goes for where you build a website.
Here is a brief overview of the different web hosting provider options out there, as well as what you should consider before signing up with one of them and building your site:
Types of Web Hosting Providers
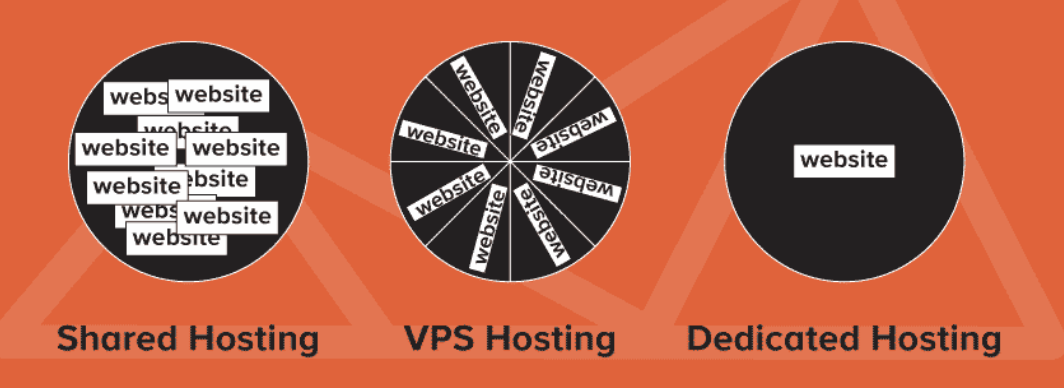
There are 3 types of web hosts to consider:
- Shared hosting: The server runs multiple websites by sharing the server and its resources with other sites. If one site on your server gets hacked, you’re at risk.
- VPS hosting: You get a Virtual Private Server. This means you share a server with other sites but you are assigned personal resources of your own. You can install personal security software to ensure you’re protected, even if others on your server aren’t.
- Dedicated hosting: The physical server runs only one website. Nothing is shared, all resources are dedicated to one website. Because of this physical division, you are not affected by hacks of any other website.
Shared Hosting
Shared hosting is the cheapest option but the least secure. If one of the sites on the server gets hacked, all the sites on the server are at risk.
If other sites on your server choose to use weak security measures or fail to regularly update their plugins, your site will suffer the consequences of slowdowns and downtime. These gaps and loopholes allow hackers to easily gain access to the entire server. Once in, they can easily delete websites and databases and infect all the sites on the server.
Be vigilant in asking about what security measures the host provider has in place.
Many shared hosting providers will allow you to cage your sites, which adds some security. This is done using auto installers that cage or segregate each site on the same server.
Remember though, regardless of what security measures you take with a shared hosting environment, it’s not possible to ensure100 percent protection to you site.
Fixing a virus in shared hosting is a nightmare. As the virus can spread like wildfire and if a single account clean-up is overlooked, the system will be on its knees again.
Shared hosting is often rebranded as “cloud hosting”. It is important to know that there is no fluffy cloud. It’s just someone else’s computer in a data centre.
VPS Hosting
VPS hosting is a closed environment and far more secure than shared hosting but does cost a bit more.
With VPS you are still sharing a server – even if you have a partition. There are other websites on that same server so there is still a chance, even if it is a small one, that your website will be affected if another website is hogging a bunch of resources. Security breaches are much easier to fix on a VPS.
It is important that the host provider regularly updates your server software. You also must take responsibility for your own website security, which we will discuss soon.
Dedicated Hosting
Dedicated hosting is the most secure and expensive option. If you have the budget, there are many advantages of choosing a dedicated hosting provider.
The main advantage being that you are not sharing your resources with other users. Although they can host multiple websites that are controlled by the same user or company.
Dedicated hosting is worth considering if you have an e-commerce site that transmits personal information through their payment processing. They are also the best option for sites that hold confidential information.
Remember though, nothing is 100% safe and you must take responsibility for your own website security as well.
Things To Look For In A Web Hosting Provider
Server log availability
A server log file is a simple text document that contains all activities of a specific server. This data includes server errors and user access records along with a host of additional data. They can be used to pinpoint security issues. They also provide a conclusive investigation that can be used if your site is attacked.
Server logs are an essential piece of data because they contain information that cannot be found anywhere else. For example, server errors and user access records along with a host of additional data. Having the ability to review these logs gives you the ability to determine what caused an issue on your server. You can also use them to pinpoint a potential security issue. Without server logs, you are left without a way to determine what is going on with your servers.
A good hosting plan will offer instant access to all logs within the past 24 hours on the server. You should ask your hosting provider how long the log archives are kept for. The number will vary from 30 days to 2 years.

Data Backup, restore points, and redundant hardware backups
Extra server banks called Redundant hardware backups carry a mirror of the data that’s on the current version of the live server. In the event of a hardware failure, the redundant server can be deployed to either take the place of the production server or share its traffic load to minimise problems.
Backups are the quickest mode to restore a hacked website. Data backups are a standard for every hosting provider. How often your site is backed up depends on the hosting plan and your needs. Your business may need hourly back-ups whereas other businesses many only require daily back-ups. In addition to those backups, a string of restore points give you a point of jumping back to a prior version – before the breach occurred.
A good hosting provider will listen to your situation and the types of data that you store and advice on best practices for backups. It is important to have a clear understanding of the process and how long it could take to get your data back if you need it.
You can also take your own backup of the website and store it on a remote or portable hard drive. Although this may be seen as overkill, it does allow the website owner the ability to move the website rapidly to a new hosting platform if the current host is compromised.
Other Must-Haves
Make sure your web hosting provider can check most, if not all, of the boxes below:
- Carefully screens the identity of new clients by requiring proof of identity (especially if you are on a shared plan).
- Has a reliable firewall to block any threat from outside the network.
- Has software that prevents DDoS attack on servers. This should be a must to all hosting solutions.
- Limits use of executable commands as these can be used to access files throughout the server network.
- Constantly monitors against malicious code uploads.
- On-site security protocols at the data center
- Suspends sites where threat is found and will only be allowed to function when threat is removed.
- If possible, encrypt data being uploaded so as not to compromise it during the upload, with the use of SFTP.

Leave a comment